A deadline for Indigo Books to pay a ransom or risk the public release of employee personal information has come and gone without the stolen data being made public, but a privacy advocate and cybersecurity analyst both say this doesn’t mean there’s any less risk for Canadians affected by the data breach.
On Wednesday night, Canada’s largest bookstore chain said it would not agree to payment demands from an online group claiming affiliation with ransomware site LockBit, because it could not guarantee the money wouldn’t “end up in the hands of terrorists.”
The hacker group indicated it would be posting all the stolen information publicly and a countdown timer posted on multiple versions of the LockBit dark web forum said the data would be released on Thursday at 3:39 p.m. ET.
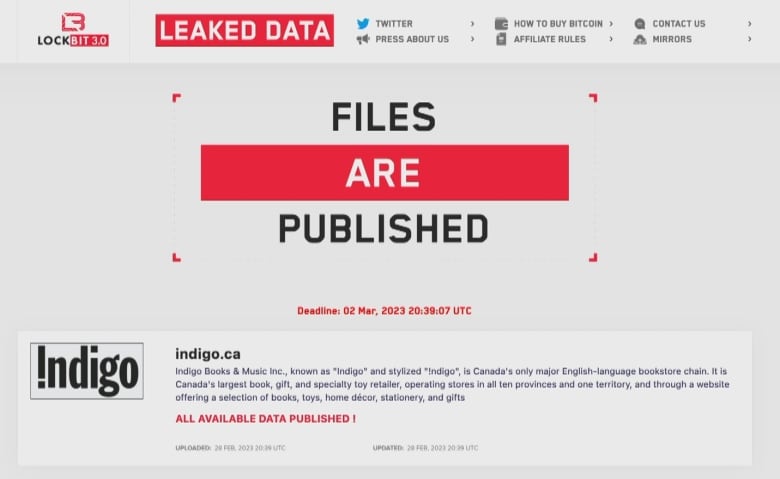
After the deadline passed on Thursday afternoon, the LockBit forums said the data had been released. However both CBC News and an independent security analyst could not find actual data available to access. CBC reached out to Indigo to confirm if it was aware if the data had been released or not, but did not hear back in time for publication.
Just because the information appears not to have been posted does not mean the data is safe or secure — and it definitely doesn’t mean the data won’t be released in the future, according to Chester Wisniewski, field chief technology officer at international cybersecurity firm Sophos.
“They are criminals, after all. They are not obligated to do anything that they say they’re going to do,” said Wisniewski, who is based in Vancouver.
He noted that it must be assumed that the employee data is compromised even if it’s not released publicly.

Multiple current and former Indigo workers have told CBC News they are worried about what happens if information such as their emails, home addresses, social insurance numbers and bank account details are made public. Indigo has previously told employees those are just some examples of some of the stolen data.
Indigo has offered some current and former employees a credit protection service for two years.
Meghan, who worked at Indigo-owned stores until 2020, fears that if her identity is ever compromised due to this stolen data, she could face consequences forever. CBC has agreed not to reveal her last name due to privacy concerns.
“There’s been no kind of assurance at all from Indigo to me or any of my former coworkers saying what their plans are,” she said in an interview Thursday morning.

The company said it “will continue to address any concerns that may arise” in a statement to CBC News on Wednesday.
But Meghan says the two-year plan to monitor her credit history isn’t enough.
“I can’t flag it years later down the line if I want to buy a house. ‘Oh, I was maybe [de]frauded years ago by a company I haven’t worked at for ten years,’ ” she said.
“It’s definitely making me a little bit more scared, I guess, thinking about the future, because this is something that will follow me potentially for the rest of my life.”
Companies must ‘inventory’ information: privacy expert
Part of why Canadians may face identity theft due to cyberattacks is because corporate entities such as Indigo keep too much information and for too long, according to Privacy and Access Council of Canada president Sharon Polsky.
“We have to look to our employers and ask why, why are you keeping this information?” she said, noting that domestic law may not be sufficient to protect Canadian data because many companies store their information on international servers, while cyber-crime organizations often operate outside of court jurisdictions.
“We can’t look to the legislation that is, at best, 20 years old and was developed before all of these technologies were even contemplated,” said Polsky.
For now, she says Canadians can try to protect themselves from identity theft by keeping track of their personal data and demanding better management from corporate entities such as employers.

“One of the things people might want to do is put in a formal access to information request to their former employer and to the companies and governments they deal with to find out what information is held about them and who it has been shared with,” she said.
“We have to all have an inventory of the information that we’ve given out,” explained Polsky, who referenced data points such as birth dates, social insurance numbers, driver’s licence numbers and home addresses.
Indigo website remains partly down
Indigo has previously said it didn’t know the identity of the group behind the attack that stole the information. LockBit has been used in previous cyberattacks, including one that targeted Toronto’s Hospital for Sick Children.
When Indigo was hit by the cyberattack on Feb. 8, its website went offline entirely and the chain’s brick-and-mortar stores were also unable to process credit, debit or gift card transactions. Physical stores were back up after the following weekend.
The website was back to taking some purchases last week but is still not offering as many products for sale as before the ransomware attack.






































Leave a comment